Evo jedan novi smišing

Još neki očigledno maliciozni domeni su na istoj IP adresi:
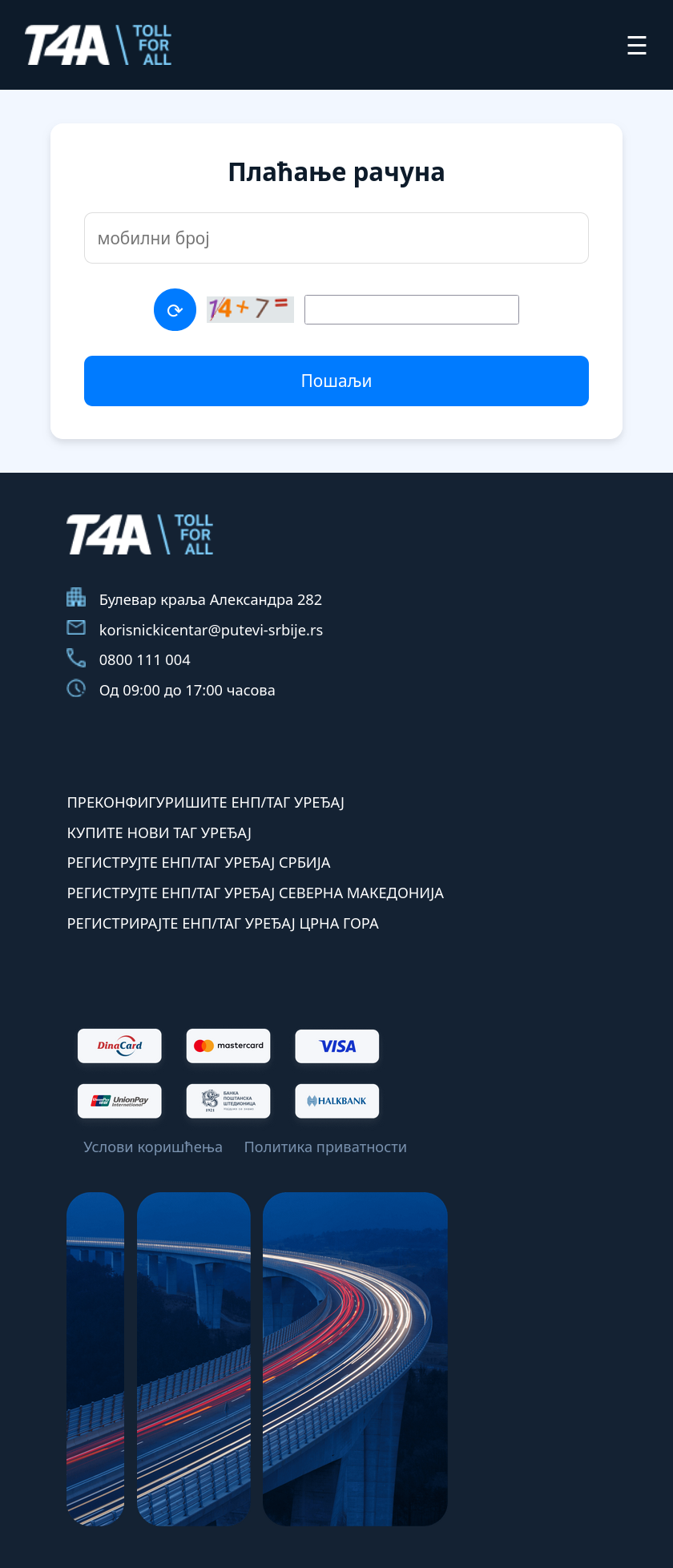
stranica izgleda ovako:
Code:
toll4all.top has address 82.29.129.191Još neki očigledno maliciozni domeni su na istoj IP adresi:
Code:
gobapp.click
plusmilesonline.top
best-buy-houses.top
nea-gov-sg.top
autopista-del-sol.icu
thetollroad.clickstranica izgleda ovako:






![[Image: eIj7JYp.png]](https://i.imgur.com/eIj7JYp.png)