Pun naziv firme: PODZEMNO SKLADIŠTE GASA BANATSKI DVOR DRUŠTVO SA OGRANIČENOM ODGOVORNOŠĆU NOVI SAD
Nema nezavisne potvrde o događaju, ali veoma je verovatan videvši da je postojalo dobro predosećanje: Na prodaju VPN pristup za srpsko transportno-skladišno preduzeće
Glavna vest: RansomHub Cyberattack Targets Serbian Gas Firm PSG BANATSKI DVOR, Disables SCADA Systems
Threat Actor Blames Employee for the PSG BANATSKI DVOR Cyberattack
Nema nezavisne potvrde o događaju, ali veoma je verovatan videvši da je postojalo dobro predosećanje: Na prodaju VPN pristup za srpsko transportno-skladišno preduzeće
Glavna vest: RansomHub Cyberattack Targets Serbian Gas Firm PSG BANATSKI DVOR, Disables SCADA Systems
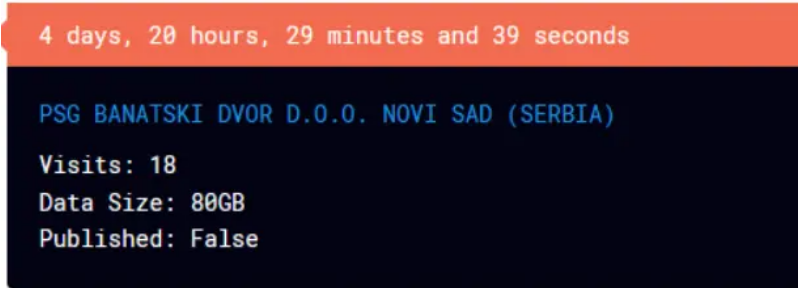
Quote:According to the threat actor post, the RansomHub exfiltrated a substantial amount of data totaling 80 GB. Among the stolen information are critical files encompassing IT, Accounting, Finance, Projects, Client database (in SQL format), Budgets, Taxes, Logistics and supply chain management, Production data, HR, Legal data, KPI, and R&D documents.
Additionally, the threat actors has allegedly disabled the SCADA (Supervisory Control and Data Acquisition) systems, further exacerbating the operational impact of the attack.
The cybercriminals have set a deadline of 5 days for the potential leak of the stolen data, adding urgency to the situation. The implications of such a breach extend beyond PSG BANATSKI DVOR, affecting not only the company but also its clients and stakeholders.
Moreover, the PSG BANATSKI DVOR website is currently nonfunctional and is displaying a “took too long to respond” error. This error, often associated with cyberattacks, suggests disruptions in the normal functioning of the website, possibly due to overwhelming server loads or exploitation of vulnerabilities in the site’s infrastructure.
Threat Actor Blames Employee for the PSG BANATSKI DVOR Cyberattack
Quote:“We have all the important files, such as: IT, Accounting, Finance, Projects, Client database (in SQL format) Budgets, Taxes, Logistics and supply chain management, Production data, HR, Legal data, KPI, R&D. Over 80 GB of sensational information has been downloaded”
Additionally, the group blames an employee named Dejan Belić for the breach. The threat actors have previously targeted similar victims and share similarities with traditional Russian ransomware groups while refraining from targeting certain countries and non-profits.




